Your business
Transformed
Your Business.
Transformed
Our aim is to realise increased growth and cost savings through digital transformation, as well as creating a greater impact on every individual connected to your business.
What makes us different from other consultancies is our team. We only employ senior experts who have years of experience tackling real-world challenges.
Our purpose is to help our clients make a better impact on the world.







Our complete
digital
infrastructure solution
We create unique turnkey solutions for digital infrastructure projects and large-scale challenges encompassing subsea, data centres, broadband infrastructure and satellite, and a broad range of services such as strategy, data & AI, project management, procurement and more.
Sign up for news and insights from Cambridge MC (no more than once a month).
Featured Capabilities
Digital Infrastructure
We empower organisations to grow by tackling the complexities of digital infrastructure, including 5G, IoT, and generative AI. Our expertise transforms both virtual and physical landscapes, enhancing data centers, carriers, subsea cables and more.
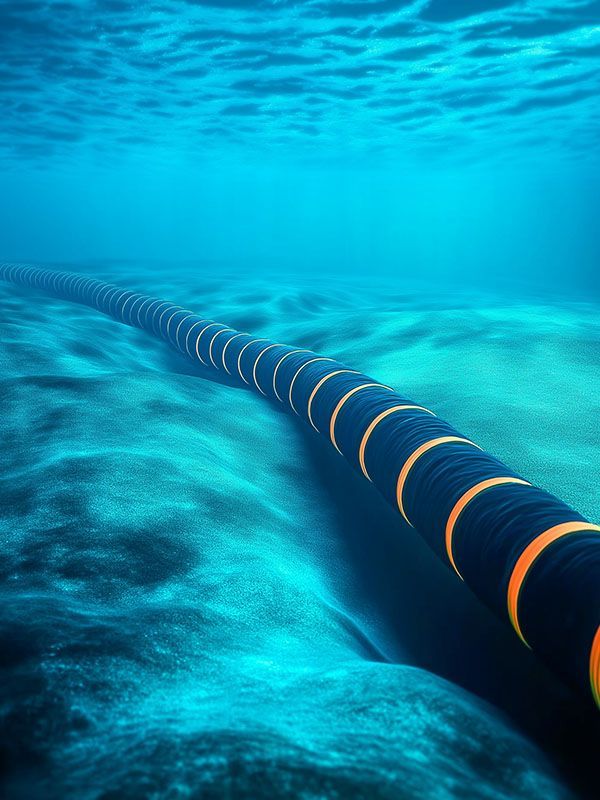
Subsea Services
We excel at research, strategy, feasibility and network deployment studies, design, procurement, system implementation & project management, operations & maintenance environment - allowing you to combine services to accomplish your strategic goals.
Broadband Infrastructure
Our Broadband Infrastructure services are designed to support the service provider community and the broader ecosystem in navigating current challenges in the market. Our service wrapper provides solutions that enable carriers and operators to optimise their network performance.
Featured Capabilities
Cyber Security
Our experts apply Secure by Design principles and work with your board and IT team on cyber strategy, architecture, and recovery plans/testing. We also provide workforce training, board buy-in services, fractional CISO, and help with accreditation and regulatory compliance.
Digital Infrastructure
We empower organisations to grow by tackling the complexities of digital infrastructure, including 5G, IoT, Edge and AI. Our experts help to transform both virtual and physical landscapes, enhancing data centres, network architecture, subsea cables and more.
Subsea Services
We excel at strategy, feasibility and network deployment studies, design, procurement, system implementation, project management, and operations — allowing you to combine the necessary services to accomplish your strategic goals.
Broadband Infrastructure
Our Broadband Infrastructure services are designed to support the service provider community and the broader ecosystem in navigating current challenges in the market. Our service wrapper provides solutions that enable carriers and operators to optimise their network performance.
Digital Transformation
To realise a return on your technology ambitions, your strategy, budget, and project management must be meticulously planned and aligned. We support businesses and the public sector through the full transformation lifecycle, with methodologies that manage risk & maximse your return on investment.
Sign up for news and insights from Cambridge MC (no more than once a month).
Featured Capabilities
Sustainability
End-to-end sustainability management that starts with your footprint and risks, and then a pragmatic strategy to implement initiatives, track performance, and produce audit-ready reports – delivering cost savings, compliance, and measurable impact. With our carbon accounting & management platform, cero.earth, you gain real-time emissions data, clear reduction pathways, and actionable insights.
Strategy
Lasting success depends on knowing where to play and how to win. Using a methodology that blends the broad and deep experience of our team with research and data analytics, we help organisations align leadership vision, culture, and execution to enhance their competitive edge and create sustained growth on a local or global stage.
Procurement & Commercial
We help unlock value, reduce risk, and accelerate delivery through smarter procurement strategies. Our experts draw on market insights and their own experience to optimise supplier relationships, cut costs, and strengthen governance. From sourcing strategy to contract negotiation & performance management, we ensure your investment delivers measurable impact.
Artificial Intelligence & Data
A full AI production line, from strategy and readiness assessment, through implementation, to scaling and optimisation. Our industry experts help you align AI initiatives with business goals, upskill your workforce, and ensure ethical, compliant, and effective deployments.
Digital Transformation
From discovery to scaled delivery, we modernise processes, platforms, and operating models. We streamline customer journeys, automate workflows, migrate to cloud, and embed data & AI. We govern change with robust PMO and benefits tracking. The result is faster time-to-value, lower cost-to-serve, resilient architectures, and teams equipped to keep improving.
Digital Infrastructure
We help organisations to grow sustainably by tackling the complexities of digital infrastructure, including 5G, IoT, Edge and AI. Our experts help to transform both virtual and physical landscapes – enhancing data centres, network architecture, subsea cables and more.
Preparing for the PSTN Switch-Off: Insights & Actions to Shape Your Strategy
Discover key strategies and insights to help plan your transition strategy for 31 January 2027 — no matter your sector, industry, or size.

Case Studies
Our team has had the privilege of partnering with a diverse array of clients, from burgeoning startups to FTSE 100
companies. Each case study reflects our commitment to delivering tailored solutions that drive real business results.
CASE STUDIES
A little bit about Cambridge MC
Cambridge Management Consulting is a specialist consultancy drawing on an extensive global network of over 200 senior executives in 22 countries.
Our purpose is to help our clients make a better impact on the world.
ABOUT CAMBRIDGE MC
Latest
Case Studies
Latest
Case Studies
Discover how our team has successfully transformed organisations with innovative solutions, driving growth and enhancing competitive advantage across diverse industries.
Big Data & Machine Learning
Using data analytics to accelerate network transformation
Validating a Business Case
Analysing and validating a critical business case to ensure its accuracy and feasibility
Latest
Case Studies
Discover how our team has successfully transformed organisations with innovative solutions, driving growth and enhancing competitive advantage across diverse industries.
Latest insights

Cyber Security
Our experts apply Secure by Design principles and work with your board and IT team on cyber strategy, architecture, and recovery plans/testing. We also provide workforce training, board buy-in services, fractional CISO, and help with accreditation and regulatory compliance.
Digital Infrastructure
We empower organisations to grow by tackling the complexities of digital infrastructure, including 5G, IoT, Edge and AI. Our experts help to transform both virtual and physical landscapes, enhancing data centres, network architecture, subsea cables and more.
Subsea Services
We excel at strategy, feasibility and network deployment studies, design, procurement, system implementation, project management, and operations — allowing you to combine the necessary services to accomplish your strategic goals.
Broadband Infrastructure
Our Broadband Infrastructure services are designed to support the service provider community and the broader ecosystem in navigating current challenges in the market. Our service wrapper provides solutions that enable carriers and operators to optimise their network performance.
Digital Transformation
To realise a return on your technology ambitions, your strategy, budget, and project management must be meticulously planned and aligned. We support businesses and the public sector through the full transformation lifecycle, with methodologies that manage risk & maximse your return on investment.